NEWYou can now hearken to Fox News articles!
Google designed Fast Pair to make Bluetooth connections quick and easy. One faucet replaces menus, codes and guide pairing. That comfort now comes with severe danger. Security researchers at KU Leuven uncovered flaws in Google’s Fast Pair protocol that permits silent machine takeovers. They named the assault methodology WhisperPair. An attacker close by can connect with headphones, earbuds or audio system with out the proprietor understanding. In some instances, the attacker may monitor the person’s location. Even extra regarding, victims don’t want to make use of Android or personal any Google merchandise. iPhone customers are additionally affected.
Sign up for my FREE CyberGuy Report
Get my finest tech suggestions, pressing safety alerts, and unique offers delivered straight to your inbox. Plus, you’ll get instantaneous entry to my Ultimate Scam Survival Guide — free whenever you be part of my CYBERGUY.COM publication.
APPLE WARNS MILLIONS OF IPHONES ARE EXPOSED TO ATTACK

Fast Pair makes connecting Bluetooth headphones fast, however researchers discovered that some gadgets settle for new pairings with out correct authorization. (Kurt “CyberGuy” Knutsson)
What WhisperPair is and the way it hijacks Bluetooth gadgets
Fast Pair works by broadcasting a tool’s id to close by telephones and computer systems. That shortcut hurries up pairing. Researchers discovered that many gadgets ignore a key rule. They nonetheless settle for new pairings whereas already related. That opens the door to abuse.
Within Bluetooth vary, an attacker can silently pair with a tool in about 10 to fifteen seconds. Once related, they will interrupt calls, inject audio or activate microphones. The assault doesn’t require specialised {hardware} and will be carried out utilizing a typical cellphone, laptop computer, or low-cost machine like a Raspberry Pi. According to the researchers, the attacker successfully turns into the machine proprietor.
Audio manufacturers affected by the Fast Pair vulnerability
The researchers examined 17 Fast Pair suitable gadgets from main manufacturers, together with Sony, Jabra, JBL, Marshall, Xiaomi, Nothing, OnePlus, Soundcore, Logitech and Google. Most of those merchandise handed Google certification testing. That element raises uncomfortable questions on how safety checks are carried out.
How headphones can develop into monitoring gadgets
Some affected fashions create a good greater privateness difficulty. Certain Google and Sony gadgets combine with Find Hub, which makes use of close by gadgets to estimate location. If a headset has by no means been linked to a Google account, an attacker can declare it first. That permits steady monitoring of the person’s actions. If the sufferer later receives a monitoring alert, it might seem to reference their very own machine. That makes the warning simple to dismiss as an error.
GOOGLE NEST STILL SENDS DATA AFTER REMOTE CONTROL CUTOFF, RESEARCHER FINDS
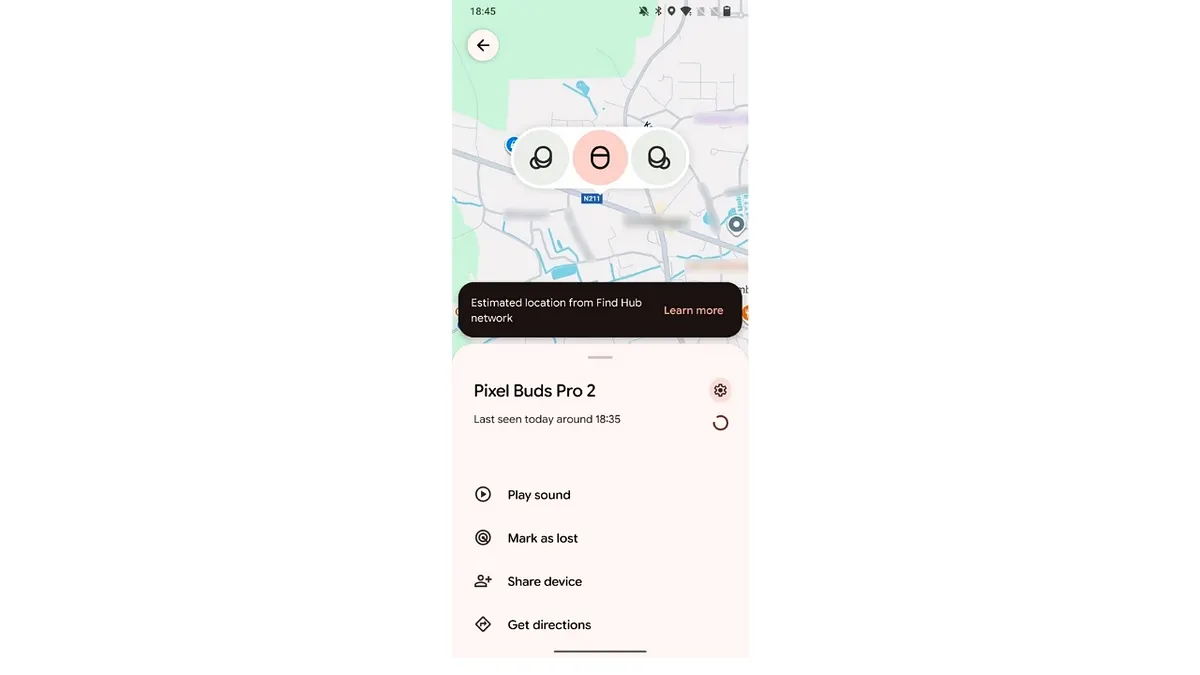
Attacker’s dashboard with location from the Find Hub community. (KU Leuven)
Why many Fast Pair gadgets might keep susceptible
There is one other downside most customers by no means contemplate. Headphones and audio system require firmware updates. Those updates normally arrive via brand-specific apps that many individuals by no means set up. If you by no means obtain the app, you by no means see the replace. That means susceptible gadgets might stay uncovered for months and even years.
The solely strategy to repair this vulnerability is by putting in a software program replace issued by the machine producer. While many corporations have launched patches, updates might not but be out there for each affected mannequin. Users ought to verify straight with the producer to verify whether or not a safety replace exists for his or her particular machine.
Why comfort retains creating safety gaps
Bluetooth itself was not the issue. The flaw lives within the comfort layer constructed on high of it. Fast Pair prioritized velocity over strict possession enforcement. Researchers argue that pairing ought to require cryptographic proof of possession. Without it, comfort options develop into assault surfaces. Security and ease of use wouldn’t have to battle. But they should be designed collectively.
Google responds to the Fast Pair WhisperPair safety flaws
Google says it has been working with researchers to handle the WhisperPair vulnerabilities and commenced sending really useful patches to headphone producers in early September. Google additionally confirmed that its personal Pixel headphones are actually patched.
In an announcement to CyberGuy, a Google spokesperson stated, “We appreciate collaborating with security researchers through our Vulnerability Rewards Program, which helps keep our users safe. We worked with these researchers to fix these vulnerabilities, and we have not seen evidence of any exploitation outside of this report’s lab setting. As a best security practice, we recommend users check their headphones for the latest firmware updates. We are constantly evaluating and enhancing Fast Pair and Find Hub security.”
Google says the core difficulty stemmed from some accent makers not totally following the Fast Pair specification. That specification requires equipment to just accept pairing requests solely when a person has deliberately positioned the machine into pairing mode. According to Google, failures to implement that rule contributed to the audio and microphone dangers recognized by the researchers.
To scale back the chance going ahead, Google says it up to date its Fast Pair Validator and certification necessities to explicitly check whether or not gadgets correctly implement pairing mode checks. Google additionally says it offered accent companions with fixes meant to completely resolve all associated points as soon as utilized.
On the placement monitoring facet, Google says it rolled out a server-side repair that stops equipment from being silently enrolled into the Find Hub community if they’ve by no means been paired with an Android machine. According to the corporate, this transformation addresses the Find Hub monitoring danger in that particular state of affairs throughout all gadgets, together with Google’s personal equipment.
Researchers, nevertheless, have raised questions on how rapidly patches attain customers and the way a lot visibility Google has into real-world abuse that doesn’t contain Google {hardware}. They additionally argue that weaknesses in certification allowed flawed implementations to achieve the market at scale, suggesting broader systemic points.
For now, each Google and the researchers agree on one key level. Users should set up producer firmware updates to be protected, and availability might range by machine and model.
SMART HOME HACKING FEARS: WHAT’S REAL AND WHAT’S HYPE
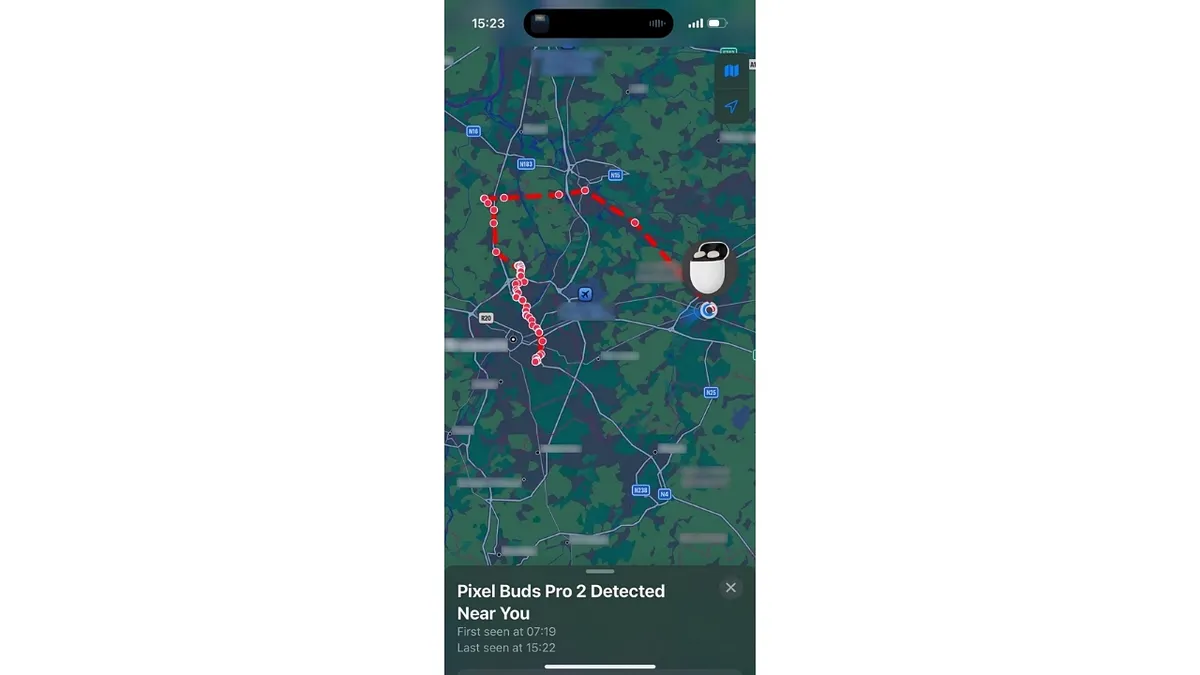
Unwanted monitoring notification exhibiting the sufferer’s personal machine. (KU Leuven)
How to scale back your danger proper now
You can’t disable Fast Pair completely, however you’ll be able to decrease your publicity.
1) Check in case your machine is affected
If you employ a Bluetooth accent that helps Google Fast Pair, together with wi-fi earbuds, headphones or audio system, it’s possible you’ll be affected. The researchers created a public lookup device that lets you seek for your particular machine mannequin and see whether or not it’s susceptible. Checking your machine is a straightforward first step earlier than deciding what actions to take. Visit whisperpair.eu/vulnerable-devices to see in case your machine is on the listing.
2) Update your audio gadgets
Install the official app out of your headphone or speaker producer. Check for firmware updates and apply them promptly.
3) Avoid pairing in public locations
Pair new gadgets in personal areas. Avoid pairing in airports, cafés or gyms the place strangers are close by.
4) Factory reset if one thing feels off
Unexpected audio interruptions, unusual sounds or dropped connections are warning indicators. A manufacturing unit reset can take away unauthorized pairings, but it surely doesn’t repair the underlying vulnerability. A firmware replace remains to be required.
5) Turn off Bluetooth when not wanted
Bluetooth solely must be on throughout lively use. Turning off Bluetooth when not in use limits publicity, but it surely doesn’t eradicate the underlying danger if the machine stays unpatched.
6) Reset secondhand gadgets
Always manufacturing unit reset used headphones or audio system earlier than pairing them. This removes hidden hyperlinks and account associations.
7) Take monitoring alerts significantly
Investigate Find Hub or Apple monitoring alerts, even when they seem to reference your personal machine.
8) Keep your cellphone up to date
Install working system updates promptly. Platform patches can block exploit paths even when equipment lag behind.
Kurt’s key takeaways
WhisperPair exhibits how small shortcuts can result in massive privateness failures. Headphones really feel innocent. Yet they include microphones, radios and software program that want care and updates. Ignoring them leaves a blind spot that attackers are blissful to take advantage of. Staying safe now means being attentive to the gadgets you as soon as took with no consideration.
Should corporations be allowed to prioritize quick pairing over cryptographic proof of machine possession? Let us know by writing to us at Cyberguy.com
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Sign up for my FREE CyberGuy Report
Get my finest tech suggestions, pressing safety alerts, and unique offers delivered straight to your inbox. Plus, you’ll get instantaneous entry to my Ultimate Scam Survival Guide — free whenever you be part of my CYBERGUY.COM publication.
Copyright 2026 CyberGuy.com. All rights reserved.
Kurt “CyberGuy” Knutsson is an award-winning tech journalist who has a deep love of expertise, gear and devices that make life higher along with his contributions for Fox News & FOX Business starting mornings on “FOX & Friends.” Got a tech query? Get Kurt’s free CyberGuy Newsletter, share your voice, a narrative concept or remark at CyberGuy.com.
